Pass the Cookie and Pivot to the Clouds
by Johann Rehberger
Web applications and services use cookies to authenticate sessions and users.
An adversary can pivot from a compromised host to web applications and Internet services by stealing authentication cookies from browsers and related processes. At the same time this technique bypasses most multi-factor authentication protocols.
The reason for this is that the final authentication token that the attacker steals is issued after all factors have been validated. Many users persist cookies that are valid for an extended period of time, even if the web application is not actively used. Cookies can be found on disk and also in process memory. Additionally, other applications on the target's machine might store sensitive authentication tokens in memory (e.g. apps which authenticate to cloud services). This pivoting technique can be extended to bearer tokens, JSON Web Token (JWT), and the likes.
Pass the Cookie is a post-exploitation technique to perform session hijacking.
So, let's Pass the Cookie and Pivot to the Clouds.
Attack Chain
Disclaimer: Always make sure you have proper authorization before pen-testing.
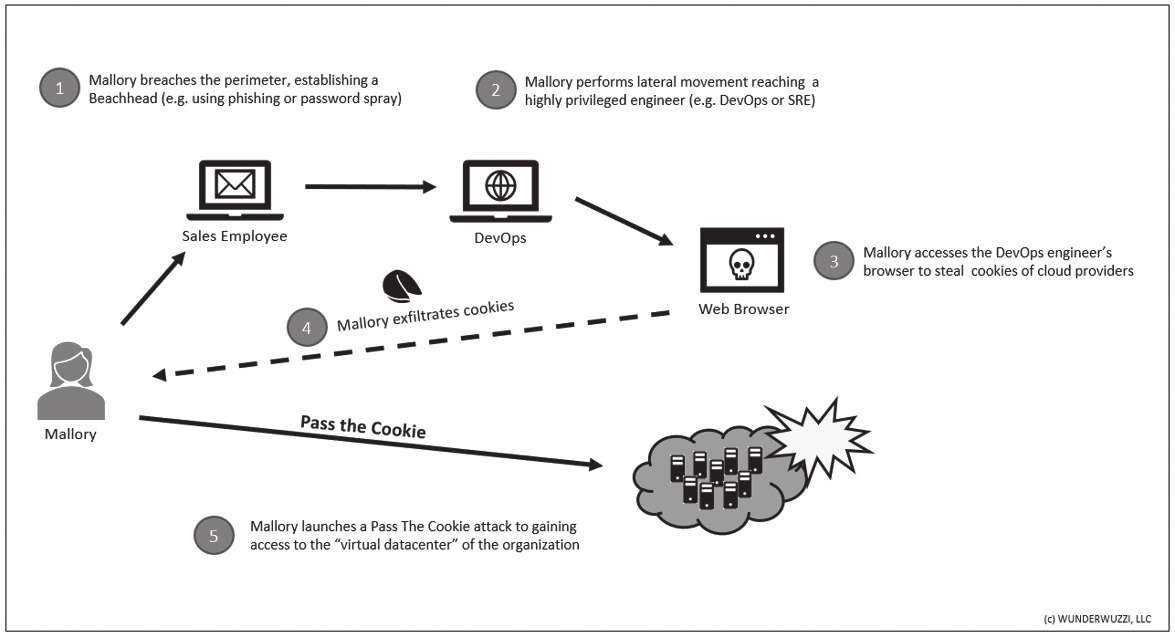
Pass the Cookie is done via the following steps (variations exist):
- Post-exploitation: Acquire the cookie from the victim's browser or other processes (e.g. via process dump, or accessing the cookie storage on disk.)
- Exfiltrate the necessary authentication cookies.
- Open Firefox on the attacker's machine (or any other machine).
- Navigate to the resource to access (the domain the cookie is valid for).
- Use the Developer Console and set the cookie via document.cookie="key=value", or use the user interface (make sure to set the domain correctly).
- Refresh the page and observe being logged in as the victim.
The following is a graphical representation during a typical red team operation, highlighting the steps:
Considering that cloud service providers for many companies are like a virtual data center, the cookie is comparable to the main entry key to the virtual facility. Pass the Cookie also works on other online services like mail, social media, etc.
Mitigations
To protect oneself from these attacks, it's important to stay up to date with security patches, etc. to ensure your host does not get compromised. As seasoned security engineer, you assume the worst. Here are some ideas on how to mitigate implications of an attack:
- Regularly delete persistent cookies so they get removed from the hard drive to limit exposure.
- Delete session cookies as well.
- Be the only administrator on your machine.
- Leverage features that cloud providers offer (threat detection, Identity and Access Management (IAM), Role-Based Access Control (RBAC), firewalls, etc.)
- Browse sensitive sites from isolated or dedicated machines (e.g. machine used for Facebook should not be the same used for banking).
- Separation of duties.
- Disable remote access services on your machine (such as SSH, RDP, ARD).
- Requiring further authentication proof for sensitive operations can help limit the damage.
- Requiring client-side certificates makes it also more difficult to pass the cookie.
Detections
When it comes to detections, a few things come to mind:
- One can monitor, on the client side, for applications that perform process dumps on browser processes.
- Monitor for unusual activity on critical web assets (e.g. cloud provider management consoles, etc.)
- Monitor for login anomalies (location, time, unusual access patterns).
- Leverage features that cloud providers and web apps provide (threat detection, access logs, etc.)
- Perform authorized adversarial emulation in your organization to test detections.
Acquiring Cookies - Tools and Techniques
In case you don't won't to write your own toolset, there are a couple of options available to gain access to cookies:
- firefox_creds - Access the SQLLite cookie databases.
- cookie_crimes - Neat way to grab cookies from Chrome on Macs (also Windows and Linux).
- ProcDump - Swiss Army knife to dump strings from any process.
- Sniffing Traffic - e.g. using SSLKEYLOGFILE during post-exploitation, leveraging WinInet tracing.
There are also good articles online describing how to access and decrypt the cookies in the SQLLite databases, as well if you'd like to dig into more under the covers.
Conclusion
Pass the Cookie is a powerful post-exploitation technique to pivot from on-premise machines to cloud assets. It can be leveraged to bypass Multi-Factor Authentication (MFA) techniques, as the cookie is - in the end - still a single factor.
Hopefully this was helpful, so you can build better detections, improvements and tests into your infrastructure to catch malicious activity.